What's new arround internet
| Src | Date (GMT) | Titre | Description | Tags | Stories | Notes |
| 2024-04-08 15:09:15 | Faits saillants hebdomadaires, 8 avril 2024 Weekly OSINT Highlights, 8 April 2024 (lien direct) |
Last week\'s OSINT reporting reveals several key trends emerge in the realm of cybersecurity threats. Firstly, there is a notable diversification and sophistication in attack techniques employed by threat actors, ranging from traditional malware distribution through phishing emails to advanced methods like DLL hijacking and API unhooking for evading detection. Secondly, the threat landscape is characterized by the presence of various actors, including state-sponsored groups like Earth Freybug (a subset of APT41) engaging in cyberespionage and financially motivated attacks, as well as cybercrime actors orchestrating malware campaigns such as Agent Tesla and Rhadamanthys. Thirdly, the targets of these attacks span across different sectors and regions, with organizations in America, Australia, and European countries facing significant threats. Additionally, the emergence of cross-platform malware like DinodasRAT highlights the adaptability of threat actors to target diverse systems, emphasizing the need for robust cybersecurity measures across all platforms. Overall, these trends underscore the dynamic and evolving nature of cyber threats, necessitating continuous vigilance and proactive defense strategies from organizations and cybersecurity professionals. **1. [Latrodectus Loader Malware Overview](https://sip.security.microsoft.com/intel-explorer/articles/b4fe59bf)** Latrodectus is a new downloader malware, distinct from IcedID, designed to download payloads and execute arbitrary commands. It shares characteristics with IcedID, indicating possible common developers. **2. [Earth Freybug Cyberespionage Campaign](https://sip.security.microsoft.com/intel-explorer/articles/327771c8)** Earth Freybug, a subset of APT41, engages in cyberespionage and financially motivated attacks since at least 2012. The attack involved sophisticated techniques like DLL hijacking and API unhooking to deploy UNAPIMON, evading detection and enabling malicious commands execution. **3. [Agent Tesla Malware Campaign](https://sip.security.microsoft.com/intel-explorer/articles/cbdfe243)** Agent Tesla malware targets American and Australian organizations through phishing campaigns aimed at stealing email credentials. Check Point Research identified two connected cybercrime actors behind the operation. **4. [DinodasRAT Linux Version Analysis](https://sip.security.microsoft.com/intel-explorer/articles/57ab8662)** DinodasRAT, associated with the Chinese threat actor LuoYu, is a cross-platform backdoor primarily targeting Linux servers. The latest version introduces advanced evasion capabilities and is installed to gain additional footholds in networks. **5. [Rhadamanthys Information Stealer Malware](https://sip.security.microsoft.com/intel-explorer/articles/bf8b5bc1)** Rhadamanthys utilizes Google Ads tracking to distribute itself, disguising as popular software installers. After installation, it injects into legitimate Windows files for data theft, exploiting users through deceptive ad redirects. **6. [Sophisticated Phishing Email Malware](https://sip.security.microsoft.com/intel-explorer/articles/abfabfa1)** A phishing email campaign employs ZIP file attachments leading to a series of malicious file downloads, culminating in the deployment of PowerShell scripts to gather system information and download further malware. **7. [AceCryptor Cryptors-as-a-Service (CaaS)](https://sip.security.microsoft.com/intel-explorer/articles/e3595388)** AceCryptor is a prevalent cryptor-as-a-service utilized in Rescoms campaigns, particularly in European countries. Threat actors behind these campaigns abuse compromised accounts to send spam emails, aiming to obtain credentials for further attacks. ## Learn More For the latest security research from the Microsoft Threat Intelligence community, check out the Microsoft Threat Intelligence Blog: [https://aka.ms/threatintelblog](https://aka.ms/threatintelblog). Microsoft customers can use the following reports in Microsoft Defender Threat Intelligence to ge | Ransomware Spam Malware Tool Threat Cloud | APT 41 | ★★★ | |
| 2024-04-03 20:46:53 | Earth Freybug Uses UNAPIMON for Unhooking Critical APIs (lien direct) | #### Description
Trend Micro a analysé une attaque de cyberespionnage que la société a attribuée à Earth Freybug, un sous-ensemble d'APT41 (suivi par Microsoft comme [typhon en laiton] (https: // sip.security.microsoft.com/intel-profiles/f0aaa62bfbaf3739bb92106688e6a00fc05afc0d4158b0e389b4078112d37c6?)).Selon Trend Micro, Earth Freybug est actif depuis àAu moins 2012 et le groupe lié au chinois a été actif dans l'espionnage et les attaques financièrement motivées.Earth Freybug utilise divers outils tels que Lolbins et les logiciels malveillants personnalisés, ciblant les organisations à l'échelle mondiale.L'attaque a utilisé des techniques telles que Dynamic Link Library (DLL) détournement et décrocheur API pour éviter la surveillance d'un nouveau malware appelé Unapimon.Unapimon élude la détection en empêchant les processus enfants d'être surveillés.
Le flux d'attaque a consisté à créer des tâches planifiées à distance et à exécuter des commandes de reconnaissance pour recueillir des informations système.Par la suite, une porte dérobée a été lancée à l'aide d'un chargement latéral DLL via un service appelé sessionnv, qui charge une DLL malveillante.Unapimon, la DLL injectée, utilise le crochet de l'API pour échapper à la surveillance et à l'exécution de commandes malveillantes non détectées, présentant les attaquants \\ 'sophistication.
[Consultez la rédaction de Microsoft \\ sur Dynamic-Link Library (DLL) Rijacking ici.] (Https://sip.security.microsoft.com/intel-explorer/articles/91be20e8?)
#### URL de référence (s)
1. https://www.trendmicro.com/en_us/research/24/d/arth-freybug.html
#### Date de publication
2 avril 2024
#### Auteurs)
Christopher So
#### Description Trend Micro analyzed a cyberespionage attack the company has attributed to Earth Freybug, a subset of APT41 (tracked by Microsoft as [Brass Typhoon](https://sip.security.microsoft.com/intel-profiles/f0aaa62bfbaf3739bb92106688e6a00fc05eafc0d4158b0e389b4078112d37c6?)). According to Trend Micro, Earth Freybug has been active since at least 2012 and the Chinese-linked group has been active in espionage and financially motivated attacks. Earth Freybug employs diverse tools like LOLBins and custom malware, targeting organizations globally. The attack used techniques like dynamic link library (DLL) hijacking and API unhooking to avoid monitoring for a new malware called UNAPIMON. UNAPIMON evades detection by preventing child processes from being monitored. The attack flow involved creating remote scheduled tasks and executing reconnaissance commands to gather system information. Subsequently, a backdoor was launched using DLL side-loading via a service called SessionEnv, which loads a malicious DLL. UNAPIMON, the injected DLL, uses API hooking to evade monitoring and execute malicious commands undetected, showcasing the attackers\' sophistication. [Check out Microsoft\'s write-up on dynamic-link library (DLL) hijacking here.](https://sip.security.microsoft.com/intel-explorer/articles/91be20e8?) #### Reference URL(s) 1. https://www.trendmicro.com/en_us/research/24/d/earth-freybug.html #### Publication Date April 2, 2024 #### Author(s) Christopher So |
Malware Tool Prediction | APT 41 | ★★ | |
| 2023-10-04 20:39:00 | Les chercheurs relient DragOnegg Android Spyware à LightSpy iOS Surveillanceware Researchers Link DragonEgg Android Spyware to LightSpy iOS Surveillanceware (lien direct) |
De nouvelles découvertes ont identifié des connexions entre un logiciel espion Android appelé DragOnegg etUn autre outil sophistiqué modulaire de surveillance iOS nommé LightSpy.
DragOnegg, aux côtés de Wyrmspy (aka AndroidControl),a été divulgué pour la première fois par Lookout en juillet 2023 comme une souche de logiciels malveillants capables de collecter des données sensibles à partir d'appareils Android.Il a été attribué au groupe national chinois Apt41.
Sur
New findings have identified connections between an Android spyware called DragonEgg and another sophisticated modular iOS surveillanceware tool named LightSpy. DragonEgg, alongside WyrmSpy (aka AndroidControl), was first disclosed by Lookout in July 2023 as a strain of malware capable of gathering sensitive data from Android devices. It was attributed to the Chinese nation-state group APT41. On |
Malware Tool | APT 41 APT 41 | ★★★ | |
| 2023-10-04 15:30:00 | Lightspy iPhone Spyware lié au groupe chinois APT41 LightSpy iPhone Spyware Linked to Chinese APT41 Group (lien direct) |
ThreatFabric a trouvé des preuves que Lighspy est lié à Android Spyware DragOnegg, attribué au groupe parrainé par les Chinois
ThreatFabric found evidence that LighSpy is linked to Android spyware DragonEgg, attributed to the Chinese-sponsored group |
APT 41 APT 41 | ★★ | ||
| 2023-09-27 12:51:29 | Les lacunes de sécurité et de confidentialité SMS montrent clairement que les utilisateurs ont besoin d'une mise à niveau de messagerie SMS Security & Privacy Gaps Make It Clear Users Need a Messaging Upgrade (lien direct) |
Posted by Eugene Liderman and Roger Piqueras Jover
SMS texting is frozen in time.
People still use and rely on trillions of SMS texts each year to exchange messages with friends, share family photos, and copy two-factor authentication codes to access sensitive data in their bank accounts. It\'s hard to believe that at a time where technologies like AI are transforming our world, a forty-year old mobile messaging standard is still so prevalent.
Like any forty-year-old technology, SMS is antiquated compared to its modern counterparts. That\'s especially concerning when it comes to security.
The World Has Changed, But SMS Hasn\'t Changed With It
According to a recent whitepaper from Dekra, a safety certifications and testing lab, the security shortcomings of SMS can notably lead to:
SMS Interception: Attackers can intercept SMS messages by exploiting vulnerabilities in mobile carrier networks. This can allow them to read the contents of SMS messages, including sensitive information such as two-factor authentication codes, passwords, and credit card numbers due to the lack of encryption offered by SMS.
SMS Spoofing: Attackers can spoof SMS messages to launch phishing attacks to make it appear as if they are from a legitimate sender. This can be used to trick users into clicking on malicious links or revealing sensitive information. And because carrier networks have independently developed their approaches to deploying SMS texts over the years, the inability for carriers to exchange reputation signals to help identify fraudulent messages has made it tough to detect spoofed senders distributing potentially malicious messages.
These findings add to the well-established facts about SMS\' weaknesses, lack of encryption chief among them.
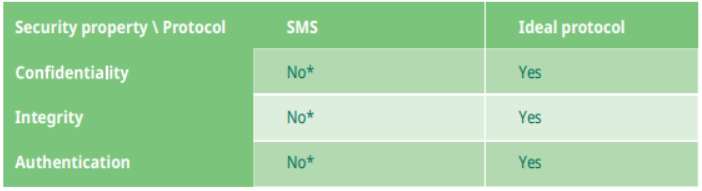
Dekra also compared SMS against a modern secure messaging protocol and found it lacked any built-in security functionality. According to Dekra, SMS users can\'t answer \'yes\' to any of the following basic security questions:
Confidentiality: Can I trust that no one else can read my SMSs?
Integrity: Can I trust that the content of the SMS that I receive is not modified?
Authentication: Can I trust the identity of the sender of the SMS that I receive?
 But this isn\'t just theoretical: cybercriminals have also caught on to the lack of security protections SMS provides and have repeatedly exploited its weakness. Both novice hackers and advanced threat actor groups (such as UNC3944 / Scattered Spider and APT41 investigated by Mandiant, part of Google Cloud) leverage the security deficiencies in SMS to launch different
But this isn\'t just theoretical: cybercriminals have also caught on to the lack of security protections SMS provides and have repeatedly exploited its weakness. Both novice hackers and advanced threat actor groups (such as UNC3944 / Scattered Spider and APT41 investigated by Mandiant, part of Google Cloud) leverage the security deficiencies in SMS to launch different |
Vulnerability Threat Studies | APT 41 | ★★★ | |
| 2023-07-20 09:34:15 | Lookout découvre un logiciel de surveillance Android avancée lié à l'APT41 de la Chine Lookout Uncovers Advanced Android Surveillanceware Linked To China\\'s APT41 (lien direct) |
Hier, Lookout, Inc., a annoncé la découverte de logiciels de surveillance Android sophistiqués connus sous le nom de Wyrmspy et Dragonegg, qui a été lié au groupe d'espionnage chinois Apt41 (aka Double Dragon, Barium et Winnti).Bien qu'il ait été inculpé de plusieurs accusations du gouvernement américain pour ses attaques contre plus de 100 entreprises privées et publiques aux États-Unis [& # 8230;]
Yesterday, Lookout, Inc., announced the discovery of sophisticated Android surveillanceware known as WyrmSpy and DragonEgg, which has been linked to the Chinese espionage group APT41 (AKA Double Dragon, BARIUM and Winnti). Despite being indicted on multiple charges by the U.S. government for its attacks on more than 100 private and public enterprises in the U.S. […] |
Mobile | APT 41 APT 41 | ★★★ | |
| 2023-07-20 07:01:12 | APT41 Hackers ciblent les utilisateurs Android avec Wyrmspy, DragOnegg Spyware APT41 hackers target Android users with WyrmSpy, DragonEgg spyware (lien direct) |
Le groupe de piratage APT41 soutenu par l'État chinois cible les appareils Android avec deux souches de logiciels espions nouvellement découvertes surnommées Wyrmspy et DragOnegg par des chercheurs en sécurité.[...]
The Chinese state-backed APT41 hacking group is targeting Android devices with two newly discovered spyware strains dubbed WyrmSpy and DragonEgg by Lookout security researchers. [...] |
APT 41 APT 41 | ★★ | ||
| 2023-07-19 20:40:00 | APT41 de Chine \\ lié à Wyrmspy, DragOnegg Mobile Spyware China\\'s APT41 Linked to WyrmSpy, DragonEgg Mobile Spyware (lien direct) |
Les États-nations voient l'opportunité de cibler directement les gens via leurs téléphones mobiles, dans ce cas avec des logiciels de surveillance Android sophistiqués.
Nation-states see the opportunity in targeting people directly through their mobile phones, in this case with sophisticated Android surveillanceware. |
APT 41 APT 41 | ★★ | ||
| 2023-07-19 19:36:00 | Les pirates liés à la Chine ciblent les appareils mobiles avec Wyrmspy et DragOnegg Spyware China-linked hackers target mobile devices with WyrmSpy and DragonEgg spyware (lien direct) |
 Le tristement célèbre groupe de piratage chinois suivi en tant qu'APT41 a utilisé deux souches de logiciels espions nouvellement identifiées pour infecter les appareils Android, ont déclaré des chercheurs en cybersécurité.APT41, également connu sous le nom de Winnti et Brass Typhoon (anciennement Barium), est un groupe d'espionnage parrainé par l'État qui a été actif pour Plus d'une décennie et est connu pour cibler les organisations gouvernementales pour le renseignement
Le tristement célèbre groupe de piratage chinois suivi en tant qu'APT41 a utilisé deux souches de logiciels espions nouvellement identifiées pour infecter les appareils Android, ont déclaré des chercheurs en cybersécurité.APT41, également connu sous le nom de Winnti et Brass Typhoon (anciennement Barium), est un groupe d'espionnage parrainé par l'État qui a été actif pour Plus d'une décennie et est connu pour cibler les organisations gouvernementales pour le renseignement
 The infamous Chinese hacking group tracked as APT41 has been using two newly-identified spyware strains to infect Android devices, cybersecurity researchers said. APT41, also known as Winnti and Brass Typhoon (formerly Barium), is a state-sponsored espionage group that has been active for more than a decade and is known for targeting government organizations for intelligence
The infamous Chinese hacking group tracked as APT41 has been using two newly-identified spyware strains to infect Android devices, cybersecurity researchers said. APT41, also known as Winnti and Brass Typhoon (formerly Barium), is a state-sponsored espionage group that has been active for more than a decade and is known for targeting government organizations for intelligence |
APT 41 APT 41 APT-C-17 | ★★ | ||
| 2023-07-19 16:00:00 | APT41 chinois lié à Wyrmspy et à DragOnegg Surveillanceware Chinese APT41 Linked to WyrmSpy and DragonEgg Surveillanceware (lien direct) |
Lookout attribué Wyrmspy et DragOnegg vers APT41 en raison de certificats de signature Android qui se chevauchent
Lookout attributed WyrmSpy and DragonEgg to APT41 due to overlapping Android signing certificates |
APT 41 APT 41 | ★★ | ||
| 2023-07-19 15:50:00 | Les pirates chinois APT41 ciblent les appareils mobiles avec de nouveaux logiciels espions Wyrmspy et DragOnegg Chinese APT41 Hackers Target Mobile Devices with New WyrmSpy and DragonEgg Spyware (lien direct) |
L'acteur prolifique lié à l'État-nation connu sous le nom d'APT41 a été lié à deux souches de logiciels spymétriques Android auparavant sans papiers appelés Wyrmspy et DragOnegg.
"Connu pour son exploitation d'applications orientées Web et son infiltration des appareils de point de terminaison traditionnels, un acteur de menace établi comme APT 41, y compris le mobile dans son arsenal de logiciels malveillants, montre comment les points de terminaison mobiles sont à grande valeur
The prolific China-linked nation-state actor known as APT41 has been linked to two previously undocumented strains of Android spyware called WyrmSpy and DragonEgg. "Known for its exploitation of web-facing applications and infiltration of traditional endpoint devices, an established threat actor like APT 41 including mobile in its arsenal of malware shows how mobile endpoints are high-value |
Malware Threat | APT 41 APT 41 | ★★ | |
| 2023-07-19 12:04:07 | Lookout découvre un logiciel de surveillance Android avancé attribué au groupe chinois APT41 (lien direct) | Lookout découvre un logiciel de surveillance Android avancé attribué au groupe chinois APT41 Un groupe de hackers établi comme l'APT41 et se concentrant sur les appareils mobiles montre comment les terminaux mobiles sont des cibles de grande valeur avec des données professionnelles et personnelles convoitées. - Malwares | APT 41 APT 41 | ★★★ | ||
| 2023-07-07 02:33:29 | Rapport de tendance des menaces sur les groupes APT & # 8211;Mai 2023 Threat Trend Report on APT Groups – May 2023 (lien direct) |
Les cas de grands groupes APT pour le mai 2023 réunis à partir de documents rendus publics par des sociétés de sécurité et des institutions sont comme commesuit.& # 8211;Agrius & # 8211;Andariel & # 8211;APT28 & # 8211;APT29 & # 8211;APT-C-36 (Blind Eagle) & # 8211;Camaro Dragon & # 8211;CloudWizard & # 8211;Earth Longzhi (APT41) & # 8211;Goldenjackal & # 8211;Kimsuky & # 8211;Lazarus & # 8211;Lancefly & # 8211;Oilalpha & # 8211;Red Eyes (Apt37, Scarcruft) & # 8211;Sidecopy & # 8211;Sidewinder & # 8211;Tribu transparente (APT36) & # 8211;Volt Typhoon (Silhouette de bronze) ATIP_2023_MAY_TRADEAT Rapport sur les groupes APT_20230609
The cases of major APT groups for May 2023 gathered from materials made public by security companies and institutions are as follows. – Agrius – Andariel – APT28 – APT29 – APT-C-36 (Blind Eagle) – Camaro Dragon – CloudWizard – Earth Longzhi (APT41) – GoldenJackal – Kimsuky – Lazarus – Lancefly – OilAlpha – Red Eyes (APT37, ScarCruft) – SideCopy – SideWinder – Transparent Tribe (APT36) – Volt Typhoon (Bronze Silhouette) ATIP_2023_May_Threat Trend Report on APT Groups_20230609 |
Threat Prediction | APT 41 APT 38 APT 37 APT 37 APT 29 APT 29 APT 28 APT 28 APT 36 APT 36 Guam Guam APT-C-17 APT-C-17 GoldenJackal GoldenJackal APT-C-36 | ★★★ | |
| 2023-05-03 18:57:00 | Groupe de pirates chinois Earth Longzhi refait surface avec des tactiques de logiciels malveillants avancés Chinese Hacker Group Earth Longzhi Resurfaces with Advanced Malware Tactics (lien direct) |
Une tenue de piratage chinoise parrainée par l'État a refait surface avec une nouvelle campagne ciblant le gouvernement, les soins de santé, la technologie et les entités manufacturières basées à Taïwan, en Thaïlande, aux Philippines et aux Fidji après plus de six mois sans activité.
Trend Micro a attribué l'ensemble d'intrusion à un groupe de cyber-espionnage qu'il suit sous le nom de Terre Longzhi, qui est un sous-groupe au sein de l'APT41 (alias Hoodoo
A Chinese state-sponsored hacking outfit has resurfaced with a new campaign targeting government, healthcare, technology, and manufacturing entities based in Taiwan, Thailand, the Philippines, and Fiji after more than six months of no activity. Trend Micro attributed the intrusion set to a cyber espionage group it tracks under the name Earth Longzhi, which is a subgroup within APT41 (aka HOODOO |
Malware | APT 41 | ★★ | |
| 2023-05-03 10:46:02 | Chinois Apt utilise la nouvelle technique \\ 'Stack Rubling \\' pour désactiver les logiciels de sécurité Chinese APT Uses New \\'Stack Rumbling\\' Technique to Disable Security Software (lien direct) |
Un sous-groupe du groupe de pirates lié à la Chine APT41 utilise une nouvelle technique \\ 'stack grond \' DOS pour désactiver les logiciels de sécurité.
A subgroup of China-linked hacker group APT41 is using a new \'stack rumbling\' DoS technique to disable security software. |
APT 41 | ★★ | ||
| 2023-05-02 21:58:00 | Sous-groupes APT41 laboure à travers l'Asie-Pacifique, en utilisant des tactiques furtives en couches APT41 Subgroup Plows Through Asia-Pacific, Utilizing Layered Stealth Tactics (lien direct) |
L'APT chinois notoire propage la cyber-malveillance autour de l'Asie du Sud-Est, et ses prochaines cibles sont déjà en vue.
The notorious Chinese APT is spreading cyber maliciousness around Southeast Asia, and its next targets are already in sight. |
APT 41 APT 41 | ★★ | ||
| 2023-05-02 00:00:00 | Attaque contre les titans de sécurité: la Terre Longzhi revient avec de nouvelles astuces Attack on Security Titans: Earth Longzhi Returns With New Tricks (lien direct) |
Après des mois de dormance, la Terre Longzhi, un sous-groupe de groupe avancé de menace persistante (APT), APT41, a réapparu avec de nouvelles techniques dans sa routine d'infection.Cette entrée de blog préfère les lecteurs de la résilience de la Terre Longzhi \\ comme une menace remarquable.
After months of dormancy, Earth Longzhi, a subgroup of advanced persistent threat (APT) group APT41, has reemerged using new techniques in its infection routine. This blog entry forewarns readers of Earth Longzhi\'s resilience as a noteworthy threat. |
Threat | APT 41 | ★★ | |
| 2023-04-18 17:58:00 | APT41 Taps Google Red Teaming Tool dans les attaques de vol d'informations ciblées APT41 Taps Google Red Teaming Tool in Targeted Info-Stealing Attacks (lien direct) |
Le groupe APT41 lié à la Chine a ciblé une organisation médiatique taïwanaise et une agence d'emploi italienne avec des outils de test de pénétration standard et open source, dans un changement de stratégie.
China-linked APT41 group targeted a Taiwanese media organization and an Italian job agency with standard, open source penetration test tools, in a change in strategy. |
Tool | APT 41 APT 41 | ★★★ | |
| 2023-04-17 17:16:00 | Google découvre l'utilisation par APT41 \\ de l'outil GC2 open source pour cibler les médias et les sites d'emploi Google Uncovers APT41\\'s Use of Open Source GC2 Tool to Target Media and Job Sites (lien direct) |
Un groupe chinois de l'État-nation a ciblé une organisation médiatique taïwanaise anonyme pour fournir un outil d'association rouge open source connu sous le nom de Google Command and Control (GC2) au milieu d'une abus plus large de l'infrastructure de Google \\ pour les fins malveillantes.
Le groupe d'analyse des menaces du géant de la technologie (TAG) a attribué la campagne à un acteur de menace qu'il suit en vertu du hoodoo de surnom géologique et géographique, qui est
A Chinese nation-state group targeted an unnamed Taiwanese media organization to deliver an open source red teaming tool known as Google Command and Control (GC2) amid broader abuse of Google\'s infrastructure for malicious ends. The tech giant\'s Threat Analysis Group (TAG) attributed the campaign to a threat actor it tracks under the geological and geographical-themed moniker HOODOO, which is |
Tool Threat | APT 41 APT 41 | ★★★ | |
| 2023-02-28 16:10:00 | China\'s BlackFly Targets Materials Sector in \'Relentless\' Quest for IP (lien direct) | Separate attacks on two subsidiaries of an Asian conglomerate reflect a surge of cyber-espionage activity in the region in the last 12 months. | APT 41 | ★★★ | ||
| 2022-11-15 08:46:34 | Previously undetected Earth Longzhi APT group is a subgroup of APT41 (lien direct) | >Trend Micro reported that the Earth Longzhi group, a previously undocumented subgroup of APT41, targets Ukraine and Asian Countries. Early this year, Trend Micro investigated a security breach suffered by a company in Taiwan. Threat actors employed a custom Cobalt Strike loader in the attack. Further analysis, revealed that the same threat actor targeted multiple regions […] | Threat Guideline | APT 41 | ★★★★ | |
| 2022-11-14 18:33:00 | New "Earth Longzhi" APT Targets Ukraine and Asian Countries with Custom Cobalt Strike Loaders (lien direct) | Entities located in East and Southeast Asia as well as Ukraine have been targeted at least since 2020 by a previously undocumented subgroup of APT41, a prolific Chinese advanced persistent threat (APT). Cybersecurity firm Trend Micro, which christened the espionage crew Earth Longzhi, said the actor's long-running campaign can be split into two based on the toolset deployed to attack its victims | Threat Guideline | APT 41 | ★★ | |
| 2022-11-09 00:00:00 | Hack the Real Box: APT41\'s New Subgroup Earth Longzhi (lien direct) | We looked into the campaigns deployed by a new subgroup of advanced persistent threat (APT) group APT41, Earth Longzhi. This entry breaks down the technical details of the campaigns in full as presented at HITCON PEACE 2022 in August. | Threat Guideline | APT 41 | ||
| 2022-11-01 15:00:00 | Anomali Cyber Watch: Active Probing Revealed ShadowPad C2s, Fodcha Hides Behind Obscure TLDs, Awaiting OpenSSL 3.0 Patch, and More (lien direct) | The various threat intelligence stories in this iteration of the Anomali Cyber Watch discuss the following topics: China, DDoS, OpenSSL, Ransomware, Russia, Spyware, and Ukraine. The IOCs related to these stories are attached to Anomali Cyber Watch and can be used to check your logs for potential malicious activity.
 Figure 1 - IOC Summary Charts. These charts summarize the IOCs attached to this magazine and provide a glimpse of the threats discussed.
Trending Cyber News and Threat Intelligence
Threat Analysis: Active C2 Discovery Using Protocol Emulation Part3 (ShadowPad)
(published: October 27, 2022)
ShadowPad is a custom, modular malware in use by multiple China-sponsored groups since 2015. VMware researchers analyzed the command-and-control (C2) protocol in recent ShadowPad samples. They uncovered decoding routines and protocol/port combinations such as HTTP/80, HTTP/443, TCP/443, UDP/53, and UDP/443. Active probing revealed 83 likely ShadowPad C2 servers (during September 2021 to September 2022). Additional samples communicating with this infrastructure included Spyder (used by APT41) and ReverseWindow (used by the LuoYu group).
Analyst Comment: Researchers can use reverse engineering and active probing to map malicious C2 infrastructure. At the same time, the ShadowPad malware changes the immediate values used in the packet encoding per variant, so finding new samples is crucial for this monitoring.
MITRE ATT&CK: [MITRE ATT&CK] Application Layer Protocol - T1071 | [MITRE ATT&CK] Exfiltration Over Alternative Protocol - T1048 | [MITRE ATT&CK] System Information Discovery - T1082 | [MITRE ATT&CK] Ingress Tool Transfer - T1105
Tags: detection:ShadowPad, C2, APT, China, source-country:CN, actor:APT41, actor:LuoYu, detection:Spyder, detection:ReverseWindow, TCP, HTTP, HTTPS, UDP
Raspberry Robin Worm Part of Larger Ecosystem Facilitating Pre-Ransomware Activity
(published: October 27, 2022)
The Raspberry Robin USB-drive-targeting worm is an increasingly popular infection and delivery method. Raspberry Robin works as a three-file infection: Raspberry Robin LNK file on an USB drive, Raspberry Robin DLL (aka Roshtyak) backdoor, and a heavily-obfuscated .NET DLL that writes LNKs to USB drives. Microsoft researchers analyzed several infection chains likely centered around threat group EvilCorp (aka DEV-0206/DEV-0243). Besides being the initial infection vector, Raspberry Robin was seen delivered by the Fauppod malware, which shares certain code similarities both with Raspberry Robin and with EvilCorp’s Dridex malware. Fauppod/Raspberry Robin infections were followed by additional malware (Bumblebee, Cobalt Strike, IcedID, TrueBot), and eventually led to a ransomware infection (LockBit, Clop).
Analyst Comment: Organizations are advised against enabling Autorun of removable media on Windows by default, as it allows automated activation of an inserted, Raspberry Robin-infected USB drive. Apply best practices related to credential hygiene, network segmentation, and attack surface reduction.
MITRE ATT&CK: [MITRE ATT&CK] Replicat
Figure 1 - IOC Summary Charts. These charts summarize the IOCs attached to this magazine and provide a glimpse of the threats discussed.
Trending Cyber News and Threat Intelligence
Threat Analysis: Active C2 Discovery Using Protocol Emulation Part3 (ShadowPad)
(published: October 27, 2022)
ShadowPad is a custom, modular malware in use by multiple China-sponsored groups since 2015. VMware researchers analyzed the command-and-control (C2) protocol in recent ShadowPad samples. They uncovered decoding routines and protocol/port combinations such as HTTP/80, HTTP/443, TCP/443, UDP/53, and UDP/443. Active probing revealed 83 likely ShadowPad C2 servers (during September 2021 to September 2022). Additional samples communicating with this infrastructure included Spyder (used by APT41) and ReverseWindow (used by the LuoYu group).
Analyst Comment: Researchers can use reverse engineering and active probing to map malicious C2 infrastructure. At the same time, the ShadowPad malware changes the immediate values used in the packet encoding per variant, so finding new samples is crucial for this monitoring.
MITRE ATT&CK: [MITRE ATT&CK] Application Layer Protocol - T1071 | [MITRE ATT&CK] Exfiltration Over Alternative Protocol - T1048 | [MITRE ATT&CK] System Information Discovery - T1082 | [MITRE ATT&CK] Ingress Tool Transfer - T1105
Tags: detection:ShadowPad, C2, APT, China, source-country:CN, actor:APT41, actor:LuoYu, detection:Spyder, detection:ReverseWindow, TCP, HTTP, HTTPS, UDP
Raspberry Robin Worm Part of Larger Ecosystem Facilitating Pre-Ransomware Activity
(published: October 27, 2022)
The Raspberry Robin USB-drive-targeting worm is an increasingly popular infection and delivery method. Raspberry Robin works as a three-file infection: Raspberry Robin LNK file on an USB drive, Raspberry Robin DLL (aka Roshtyak) backdoor, and a heavily-obfuscated .NET DLL that writes LNKs to USB drives. Microsoft researchers analyzed several infection chains likely centered around threat group EvilCorp (aka DEV-0206/DEV-0243). Besides being the initial infection vector, Raspberry Robin was seen delivered by the Fauppod malware, which shares certain code similarities both with Raspberry Robin and with EvilCorp’s Dridex malware. Fauppod/Raspberry Robin infections were followed by additional malware (Bumblebee, Cobalt Strike, IcedID, TrueBot), and eventually led to a ransomware infection (LockBit, Clop).
Analyst Comment: Organizations are advised against enabling Autorun of removable media on Windows by default, as it allows automated activation of an inserted, Raspberry Robin-infected USB drive. Apply best practices related to credential hygiene, network segmentation, and attack surface reduction.
MITRE ATT&CK: [MITRE ATT&CK] Replicat |
Ransomware Malware Hack Tool Vulnerability Threat Guideline | APT 41 | ||
| 2022-10-26 09:00:00 | Pro-PRC Dragonbridge Influencer la campagne La campagne exploite de nouveaux TTP pour cibler agressivement les intérêts américains, y compris les élections à mi-parcours Pro-PRC DRAGONBRIDGE Influence Campaign Leverages New TTPs to Aggressively Target U.S. Interests, Including Midterm Elections (lien direct) |
Mandiant a récemment observé Dragonbridge, un InfluencerCampagne Nous évaluons avec une grande confiance pour fonctionner à l'appui des intérêts politiques de la République de Chine du peuple, ciblant agressivement les États-Unis parCherchant à semer la division entre les États-Unis et ses alliés et au sein du système politique américain lui-même.Les récits récents incluent:
affirme que le China-Nexus Threat Group apt41 est plutôt un acteur soutenu par le gouvernement américain.
Tentatives agressives de discréditer le processus démocratique américain, y compris les tentatives de décourager les Américains de voter aux États-Unis
Mandiant has recently observed DRAGONBRIDGE, an influence campaign we assess with high confidence to be operating in support of the political interests of the People\'s Republic of China (PRC), aggressively targeting the United States by seeking to sow division both between the U.S. and its allies and within the U.S. political system itself. Recent narratives include: Claims that the China-nexus threat group APT41 is instead a U.S. government-backed actor. Aggressive attempts to discredit the U.S. democratic process, including attempts to discourage Americans from voting in the 2022 U.S |
Threat | APT 41 | ★★★ | |
| 2022-10-18 15:41:00 | Chinese \'Spyder Loader\' Malware Spotted Targeting Organizations in Hong Kong (lien direct) | The China-aligned espionage-focused actor dubbed Winnti has set its sights on government organizations in Hong Kong as part of an ongoing campaign dubbed Operation CuckooBees. Active since at least 2007, Winnti (aka APT41, Barium, Bronze Atlas, and Wicked Panda) is the name designated to a prolific cyber threat group that carries out Chinese state-sponsored espionage activity, predominantly | Malware Threat Guideline | APT 41 | ||
| 2022-10-18 14:15:09 | China-linked APT41 group targets Hong Kong with Spyder Loader (lien direct) | >China-linked threat actors APT41 (a.k.a. Winnti) targeted organizations in Hong Kong, in some cases remaining undetected for a year. Symantec researchers reported that cyberespionage group APT41 targeted organizations in Hong Kong in a campaign that is a likely continuation of the Operation CuckooBees activity detailed by Cybereason in May. Winnti (aka APT41, Axiom, Barium, Blackfly) is a cyberespionage […] | Threat Guideline | APT 41 APT 17 | ||
| 2022-10-18 06:00:00 | Hackers compromised Hong Kong govt agency network for a year (lien direct) | Researchers at Symantec have uncovered cyberattacks attributed to the China-linked espionage actor APT41 (a.k.a. Winnti) that breached government agencies in Hong Kong and remained undetected for a year in some cases. [...] | Guideline | APT 41 | ||
| 2022-09-20 15:00:00 | Anomali Cyber Watch: Uber and GTA 6 Were Breached, RedLine Bundle File Advertises Itself on YouTube, Supply-Chain Attack via eCommerce Fishpig Extensions, and More (lien direct) | The various threat intelligence stories in this iteration of the Anomali Cyber Watch discuss the following topics: China, Cyberespionage, Iran, Ransomware, Stealers, and Supply chain. The IOCs related to these stories are attached to Anomali Cyber Watch and can be used to check your logs for potential malicious activity.
 Figure 1 - IOC Summary Charts. These charts summarize the IOCs attached to this magazine and provide a glimpse of the threats discussed.
Trending Cyber News and Threat Intelligence
Hacker Pwns Uber Via Compromised VPN Account
(published: September 16, 2022)
On September 15, 2022, ride-sharing giant Uber started an incident response after discovering a data breach. According to Group-IB researchers, download file name artifacts point to the attacker getting access to fresh keylogger logs affecting two Uber employees from Indonesia and Brazil that have been infected with Racoon and Vidar stealers. The attacker allegedly used a compromised VPN account credentials and performed multifactor authentication fatigue attack by requesting the MFA push notification many times and then making a social-engineering call to the affected employee. Once inside, the attacker allegedly found valid credentials for privilege escalation: a PowerShell script containing hardcoded credentials for a Thycotic privileged access management admin account. On September 18, 2022, Rockstar Games’ Grand Theft Auto 6 suffered a confirmed data leak, likely caused by the same attacker.
Analyst Comment: Network defenders can consider setting up alerts for signs of an MFA fatigue attack such as a large number of MFA requests in a relatively short period of time. Review your source code for embedded credentials, especially those with administrative privileges.
MITRE ATT&CK: [MITRE ATT&CK] Valid Accounts - T1078 | [MITRE ATT&CK] Credentials from Password Stores - T1555
Tags: MFA fatigue, Social engineering, Data breach, Uber, GTA 6, GTA VI, detection:Racoon, detection:Vidar, malware-type:Keylogger, malware-type:Stealer
Self-Spreading Stealer Attacks Gamers via YouTube
(published: September 15, 2022)
Kaspersky researchers discovered a new campaign spreading the RedLine commodity stealer. This campaign utilizes a malicious bundle: a single self-extracting archive. The bundle delivers RedLine and additional malware, which enables spreading the malicious archive by publishing promotional videos on victim’s Youtube channel. These videos target gamers with promises of “cheats” and “cracks.”
Analyst Comment: Kids and other online gamers should be reminded to avoid illegal software. It might be better to use different machines for your gaming and banking activities.
MITRE ATT&CK: [MITRE ATT&CK] User Execution - T1204 | [MITRE ATT&CK] Credentials from Password Stores - T1555 | [MITRE ATT&CK] Resource Hijacking - T1496
Tags: detection:RedLine, malware-type:Stealer, Bundle, Self-spreading, Telegraph, Youtub
Figure 1 - IOC Summary Charts. These charts summarize the IOCs attached to this magazine and provide a glimpse of the threats discussed.
Trending Cyber News and Threat Intelligence
Hacker Pwns Uber Via Compromised VPN Account
(published: September 16, 2022)
On September 15, 2022, ride-sharing giant Uber started an incident response after discovering a data breach. According to Group-IB researchers, download file name artifacts point to the attacker getting access to fresh keylogger logs affecting two Uber employees from Indonesia and Brazil that have been infected with Racoon and Vidar stealers. The attacker allegedly used a compromised VPN account credentials and performed multifactor authentication fatigue attack by requesting the MFA push notification many times and then making a social-engineering call to the affected employee. Once inside, the attacker allegedly found valid credentials for privilege escalation: a PowerShell script containing hardcoded credentials for a Thycotic privileged access management admin account. On September 18, 2022, Rockstar Games’ Grand Theft Auto 6 suffered a confirmed data leak, likely caused by the same attacker.
Analyst Comment: Network defenders can consider setting up alerts for signs of an MFA fatigue attack such as a large number of MFA requests in a relatively short period of time. Review your source code for embedded credentials, especially those with administrative privileges.
MITRE ATT&CK: [MITRE ATT&CK] Valid Accounts - T1078 | [MITRE ATT&CK] Credentials from Password Stores - T1555
Tags: MFA fatigue, Social engineering, Data breach, Uber, GTA 6, GTA VI, detection:Racoon, detection:Vidar, malware-type:Keylogger, malware-type:Stealer
Self-Spreading Stealer Attacks Gamers via YouTube
(published: September 15, 2022)
Kaspersky researchers discovered a new campaign spreading the RedLine commodity stealer. This campaign utilizes a malicious bundle: a single self-extracting archive. The bundle delivers RedLine and additional malware, which enables spreading the malicious archive by publishing promotional videos on victim’s Youtube channel. These videos target gamers with promises of “cheats” and “cracks.”
Analyst Comment: Kids and other online gamers should be reminded to avoid illegal software. It might be better to use different machines for your gaming and banking activities.
MITRE ATT&CK: [MITRE ATT&CK] User Execution - T1204 | [MITRE ATT&CK] Credentials from Password Stores - T1555 | [MITRE ATT&CK] Resource Hijacking - T1496
Tags: detection:RedLine, malware-type:Stealer, Bundle, Self-spreading, Telegraph, Youtub |
Ransomware Malware Tool Vulnerability Threat Guideline | Uber Uber APT 41 APT 15 | ||
| 2022-08-19 16:30:00 | China-backed APT41 Group Hacked at Least 13 Victims in 2021 (lien direct) | The majority of the attacks spotted relied primarily on SQL injections on targeted domains | APT 41 | |||
| 2022-08-18 18:34:08 | China\'s APT41 Embraces Baffling Approach for Dropping Cobalt Strike Payload (lien direct) | The state-sponsored threat actor has switched up its tactics, also adding an automated SQL-injection tool to its bag of tricks for initial access. | Tool Threat | APT 41 | ||
| 2022-08-18 06:33:50 | China-backed APT41 Hackers Targeted 13 Organisations Worldwide Last Year (lien direct) | The Chinese advanced persistent threat (APT) actor tracked as Winnti (aka APT41) has targeted at least 13 organizations geographically spanning across the U.S, Taiwan, India, Vietnam, and China against the backdrop of four different campaigns in 2021. "The targeted industries included the public sector, manufacturing, healthcare, logistics, hospitality, education, as well as the media and | Threat Guideline | APT 41 | ★★ | |
| 2022-06-02 11:00:00 | Tendance Evil: Spotlight on Mandiant MDR Prevention of Destructive Campaies Againt Ukrainian Entities Trending Evil: Spotlight on Mandiant MDR Prevention of Destructive Campaigns Against Ukrainian Entities (lien direct) |
disponible aujourd'hui est la dernière édition de mal de tendance, Notre rapport trimestriel qui décompose leMenaces les plus récentes observées par Manialiant Managed Defense .
Dans cette édition, nous fournissons un aperçu de notre défense des entités ukrainiennes après avoir initié des mesures de protection supplémentaires pour les clients, observationsd'APT41, et une ventilation des attaques Web:
perturber les attaques russes : en prévision de la poursuiteLes cyberattaques russes à l'appui de son invasion de l'Ukraine ont géré la défense améliorée des services de surveillance et de menace pour les clients à partir de février 2022 . Cela a conduit au
Available today is the latest edition of Trending Evil, our quarterly report that breaks down the most recent threats observed by Mandiant Managed Defense. In this edition we provide an inside look at our defense of Ukrainian entities after initiating additional protective measures for customers, observations of APT41, and a breakdown of web attacks: Disrupting Russian Attacks: In anticipation of continued Russian cyber attacks in support of its invasion of Ukraine, Managed Defense enhanced monitoring and threat hunting services for customers beginning in February 2022. This led to the |
Threat | APT 41 | ★★★ | |
| 2022-05-04 22:06:34 | China-linked Winnti APT steals intellectual property from companies worldwide (lien direct) | A sophisticated cyberespionage campaign, dubbed Operation CuckooBees, conducted by the China-linked Winnti group remained undetected since at least 2019. Researchers from Cybereason uncovered a sophisticated cyberespionage campaign, dubbed Operation CuckooBees, aimed at stealing intellectual property from the victims. The campaign flew under the radar since at least 2019, it was attributed by the experts to […] | APT 41 | |||
| 2022-05-04 16:28:39 | China-Linked Winnti APT Group Silently Stole Trade Secrets for Years: Report (lien direct) | "CuckooBees" campaign operated by Chinese cyber espionage group went undetected since 2019 | APT 41 | |||
| 2022-05-04 06:04:06 | Chinese Hackers Caught Stealing Intellectual Property from Multinational Companies (lien direct) | An elusive and sophisticated cyberespionage campaign orchestrated by the China-backed Winnti group has managed to fly under the radar since at least 2019. Dubbed "Operation CuckooBees" by Israeli cybersecurity company Cybereason, the massive intellectual property theft operation enabled the threat actor to exfiltrate hundreds of gigabytes of information. Targets included technology and | Threat | APT 41 | ||
| 2022-05-04 04:01:00 | Operation CuckooBees: Deep-Dive into Stealthy Winnti Techniques (lien direct) |
 In 2021, the Cybereason Nocturnus Incident Response Team investigated multiple intrusions targeting technology and manufacturing companies located in Asia, Europe and North America. Based on the findings of our investigation, it appears that the goal behind these intrusions was to steal sensitive intellectual property for cyber espionage purposes.
In 2021, the Cybereason Nocturnus Incident Response Team investigated multiple intrusions targeting technology and manufacturing companies located in Asia, Europe and North America. Based on the findings of our investigation, it appears that the goal behind these intrusions was to steal sensitive intellectual property for cyber espionage purposes. |
APT 41 | |||
| 2022-05-04 04:00:00 | Operation CuckooBees: A Winnti Malware Arsenal Deep-Dive (lien direct) |
 In part one of this research, the Cybereason Nocturnus Incident Response Team provided a unique glimpse into the Wintti intrusion playbook, covering the techniques that were used by the group from initial compromise to stealing the data, as observed and analyzed by the Cybereason Incident Response team.
In part one of this research, the Cybereason Nocturnus Incident Response Team provided a unique glimpse into the Wintti intrusion playbook, covering the techniques that were used by the group from initial compromise to stealing the data, as observed and analyzed by the Cybereason Incident Response team. |
Malware | APT 41 | ||
| 2022-03-10 23:39:03 | APT41 Compromised Six U.S. State Government Networks (lien direct) | FortiGuard Labs is aware of a report that threat actor APT41 compromised at least six networks belonging to U.S. state governments between May 2021 and February 2022. To gain a foothold into the victim's network, the threat actor used a number of different attack vectors: exploiting vulnerable Internet facing web applications and directory traversal vulnerabilities, performing SQL injection, and conducting de-serialization attacks. The intent of APT41 appears to be reconnaissance, though how the stolen information is to be used has not yet been determined.Why is this Significant? This is significant because at least six U.S. state government systems were broken into and data exfiltration was performed by APT41 as recent as February 2022 In addition, a zero-day vulnerability in the USAHerds application (CVE-2021-44207) as well as Log4j (CVE-2021-44228), among others, were exploited in the attacksWhat's the Detail of the Attack?APT41 performed several different ways to break into the targeted networks.In one case, the group exploited a SQL injection vulnerability in a Internet-facing web application. In another case, a then previously unknown vulnerability (CVE-2021-44207) in USAHerds, which is a web application used by agriculture officials to manage animal disease control and prevention, livestock identification and movement. Also, APT41 reportedly started to exploit the infamous Log4j vulnerability (CVE-2021-44228) within hours of Proof-of-Concept (PoC) code becoming available. Patches for both vulnerabilities are available. Once successful in breaking into the victim's network, the threat actor performed reconnaissance and credential harvesting activities. What is APT41?APT41 is a threat actor who has been active since at least 2012. Also known as TA415, Double Dragon, Barium, GREF and WickedPanda, the group reportedly performs Chinese state-sponsored espionage activities. APT41 targets organizations in multiple countries across a wide range of industries, such as telecommunications, industrial and engineering and think tanks. In 2020, five alleged members of the group were charged by the U.S. Justice Department for hacking more than 100 companies in the United States.What are the Tools Used by APT41?APT41 is known to use the following tools:ASPXSpy - web shell backdoorBITSAdmin - PowerShell cmdlets for creating and managing file transfers.BLACKCOFFEE - backdoor that disguise its communications as benign traffic to legitimate websites certutil - command-line utility tool used for manipulating certification authority (CA) data and components.China Chopper - web shell backdoor that allows attacker to have remote access to an enterprise networkCobalt Strike - a commercial penetration testing tool, which allows users to perform a wide range of activitiesDerusbi - DLL backdoorEmpire - PowerShell post-exploitation agent, which provides a wide range of attack activities to usersgh0st RAT - Remote Access Trojan (RAT)MESSAGETAP - data mining malware Mimikatz - open-source credential dumpernjRAT - Remote Access Trojan (RAT)PlugX - Remote Access Trojan (RAT)PowerSploit - open-source, offensive security framework which allows users to perform a wide range of activitiesROCKBOOT - BootkitShadowPad - backdoorWinnti for Linux - Remote Access Trojan (RAT) for LinuxZxShell - Remote Access Trojan (RAT)Badpotato - open-source tool that allows elevate user rights towards System rightsDustPan - shellcode loader. aka StealthVectorDEADEYE - downloaderLOWKEY - backdoorKeyplug - backdoorWhat are Other Vulnerabilities Known to be Exploited by APT41?APT41 exploited the following, but not restricted to, these vulnerabilities in the past:CVE-2020-10189 (ManageEngine Desktop Central remote code execution vulnerability)CVE-2019-19781 (Vulnerability in Citrix Application Delivery Controller, Citrix Gateway, and Citrix SD-WAN WANOP appliance)CVE-2019-3396 (Atlassian Confluence Widget Connector Macro Velocity Template Injection)CVE-2017-11882 (Microsoft Office Memory Corruption Vulnerability)CVE-2017-0199 (Microsoft Office/WordPad Remote Code Execut | Malware Tool Vulnerability Threat Guideline | APT 41 APT 15 APT 15 | ||
| 2022-03-09 21:10:20 | APT41 Spies Broke Into 6 US State Networks via a Livestock App (lien direct) | The China-affiliated state-sponsored threat actor used Log4j and zero-day bugs in the USAHerds animal-tracking software to hack into multiple government networks. | Hack Threat | APT 41 | ||
| 2022-03-09 12:24:11 | Comment: Chinese Spies Hacked A Livestock App To Breach US State Networks (lien direct) | It has been reported that cyber researchers have revealed a long-running hacking campaign that breached at least six US state governments over the past year. Chinese cyberespionage group APT41 used a vulnerability in web-based software USAHERDS to penetrate at least two of those targets. It may have hit many more, given that 18 states run USAHERDS […] | Vulnerability Guideline | APT 41 | ||
| 2022-03-09 12:04:33 | Log4j Breaches At Least 6 U.S. State Governments (lien direct) | Following the news that the China-backed APT41 hacking group has compromised at least six US state governments by exploiting the Log4j vulnerability, cyber security experts commented below. | Guideline | APT 41 | ||
| 2022-03-09 09:30:00 | Chinese APT41 Group Compromises Six US Government Networks (lien direct) | Group exploited Log4Shell “within hours,” says Mandiant | APT 41 | |||
| 2022-03-09 07:15:00 | China\'s APT41 exploited Log4j within hours (lien direct) | Group exploited Log4Shell “within hours,” says Mandiant | APT 41 | |||
| 2022-03-09 02:04:37 | Chinese APT41 Hackers Broke into at Least 6 U.S. State Governments: Mandiant (lien direct) | APT41, the state-sponsored threat actor affiliated with China, breached at least six U.S. state government networks between May 2021 and February 2022 by retooling its attack vectors to take advantage of vulnerable internet-facing web applications. The exploited vulnerabilities included "a zero-day vulnerability in the USAHERDS application (CVE-2021-44207) as well as the now infamous zero-day in | Vulnerability Threat Guideline | APT 41 | ||
| 2022-03-08 15:00:00 | Est-ce que cela a l'air infecté?Un résumé de l'APT41 ciblant les gouvernements des États américains Does This Look Infected? A Summary of APT41 Targeting U.S. State Governments (lien direct) |
Mise à jour (8 mars): Le message d'origine n'a peut-être pas apporté la clarté totale que CVE-2021-44207 (USAHERDS) avait un correctif développé par des systèmes de renom pour les déploiements applicables sur ouVers le 15 novembre 2021. Mandiant ne peut pas parler des versions, déploiement, adoption, adoption ou d'autres facteurs techniques de ce patch de vulnérabilité au-delà de sa disponibilité.
En mai 2021, Mandiant a répondu à une intrusion APT41 ciblant un réseau informatique du gouvernement de l'État des États-Unis.Ce n'était que le début d'un aperçu de Mandiant \\ sur une campagne persistante d'un mois menée par APT41 en utilisant Internet vulnérable
UPDATE (Mar. 8): The original post may not have provided full clarity that CVE-2021-44207 (USAHerds) had a patch developed by Acclaim Systems for applicable deployments on or around Nov. 15, 2021. Mandiant cannot speak to the affected builds, deployment, adoption, or other technical factors of this vulnerability patch beyond its availability. In May 2021 Mandiant responded to an APT41 intrusion targeting a United States state government computer network. This was just the beginning of Mandiant\'s insight into a persistent months-long campaign conducted by APT41 using vulnerable Internet |
Vulnerability | APT 41 APT 41 | ★★★★ | |
| 2022-01-25 16:00:00 | Anomali Cyber Watch: MoonBounce, AccessPress, QR Code Scams and More (lien direct) | The various threat intelligence stories in this iteration of the Anomali Cyber Watch discuss the following topics: APT, Linux Malware, Supply-Chain Attacks, Malspam, Phishing, and Vulnerabilities. The IOCs related to these stories are attached to Anomali Cyber Watch and can be used to check your logs for potential malicious activity.
 Figure 1 - IOC Summary Charts. These charts summarize the IOCs attached to this magazine and provide a glimpse of the threats discussed.
Trending Cyber News and Threat Intelligence
FBI Warns Of Malicious QR Codes Used To Steal Your Money
(published: January 23, 2022)
The Federal Bureau of Investigation (FBI) recently released a notice that malicious QR codes have been found in the wild. These codes, when scanned, will redirect the victim to a site where they are prompted to enter personal and payment details. The site will then harvest these credentials for cybercriminals to commit fraud and empty bank accounts. This threat vector has been seen in Germany as of December 2021.
Analyst Comment: Always be sure to check that emails have been sent from a legitimate source, and that any financial details or method of payment is done through the website. While QR codes are useful and being used by businesses more often, it is easy for cybercriminals to perform this kind of scam. If scanning a physical QR code, ensure the code has not been replaced with a sticker placed on top of the original code. Check the final URL to make sure it is the intended site and looks authentic.
MITRE ATT&CK: [MITRE ATT&CK] Phishing - T1566
Tags: EU & UK, Banking and Finance
MoonBounce: The Dark Side Of UEFI Firmware
(published: January 20, 2022)
Kaspersky has reported that in September 2021, a bootloader malware infection had been discovered that embeds itself into UEFI firmware. The malware patches existing UEFI drivers and resides in the SPI flash memory located on the motherboard. This means that it will persist even if the hard drive is replaced. Code snippets and IP addresses link the activity to APT41, a group that is operated by a group of Chinese-speaking individuals. MoonBounce is highly sophisticated and very difficult to detect.
Analyst Comment: Systems should be configured to take advantage of Trusted Platform Module (TPM) hardware security chips to secure their systems' boot image and firmware, where available. Secure boot is also a viable option to mitigate against attacks that would patch, reconfigure, or flash existing UEFI firmware to implant malicious code.
MITRE ATT&CK: [MITRE ATT&CK] Pre-OS Boot - T1542 | [MITRE ATT&CK] Data Obfuscation - T1001 | [MITRE ATT&CK] Data Encoding - T1132 | [MITRE ATT&CK] Exploitation of Remote Services - T1210 | [MITRE ATT&CK] Remote Services - T1021 | [MITRE ATT&CK] Shared Modules - T1129 | [MITRE ATT&CK] Hijack Execution Flow - T1574 |
Figure 1 - IOC Summary Charts. These charts summarize the IOCs attached to this magazine and provide a glimpse of the threats discussed.
Trending Cyber News and Threat Intelligence
FBI Warns Of Malicious QR Codes Used To Steal Your Money
(published: January 23, 2022)
The Federal Bureau of Investigation (FBI) recently released a notice that malicious QR codes have been found in the wild. These codes, when scanned, will redirect the victim to a site where they are prompted to enter personal and payment details. The site will then harvest these credentials for cybercriminals to commit fraud and empty bank accounts. This threat vector has been seen in Germany as of December 2021.
Analyst Comment: Always be sure to check that emails have been sent from a legitimate source, and that any financial details or method of payment is done through the website. While QR codes are useful and being used by businesses more often, it is easy for cybercriminals to perform this kind of scam. If scanning a physical QR code, ensure the code has not been replaced with a sticker placed on top of the original code. Check the final URL to make sure it is the intended site and looks authentic.
MITRE ATT&CK: [MITRE ATT&CK] Phishing - T1566
Tags: EU & UK, Banking and Finance
MoonBounce: The Dark Side Of UEFI Firmware
(published: January 20, 2022)
Kaspersky has reported that in September 2021, a bootloader malware infection had been discovered that embeds itself into UEFI firmware. The malware patches existing UEFI drivers and resides in the SPI flash memory located on the motherboard. This means that it will persist even if the hard drive is replaced. Code snippets and IP addresses link the activity to APT41, a group that is operated by a group of Chinese-speaking individuals. MoonBounce is highly sophisticated and very difficult to detect.
Analyst Comment: Systems should be configured to take advantage of Trusted Platform Module (TPM) hardware security chips to secure their systems' boot image and firmware, where available. Secure boot is also a viable option to mitigate against attacks that would patch, reconfigure, or flash existing UEFI firmware to implant malicious code.
MITRE ATT&CK: [MITRE ATT&CK] Pre-OS Boot - T1542 | [MITRE ATT&CK] Data Obfuscation - T1001 | [MITRE ATT&CK] Data Encoding - T1132 | [MITRE ATT&CK] Exploitation of Remote Services - T1210 | [MITRE ATT&CK] Remote Services - T1021 | [MITRE ATT&CK] Shared Modules - T1129 | [MITRE ATT&CK] Hijack Execution Flow - T1574 | |
Ransomware Malware Tool Vulnerability Threat Guideline | APT 41 APT 28 | ||
| 2022-01-21 11:59:14 | MoonBounce UEFI implant spotted in a targeted APT41 attack (lien direct) | Researchers have spotted China-linked APT41 cyberespionage group using a UEFI implant, dubbed MoonBounce, to maintain persistence. Kaspersky researchers spotted the China-linked APT41 cyberespionage group using a UEFI implant, dubbed MoonBounce, to maintain persistence. At the end of 2021, researchers discovered a UEFI firmware-level compromise by analyzing logs from its Firmware Scanner. Threat actors compromised a single […] | Threat Guideline | APT 41 | ||
| 2022-01-21 03:40:40 | Chinese Hackers Spotted Using New UEFI Firmware Implant in Targeted Attacks (lien direct) | A previously undocumented firmware implant deployed to maintain stealthy persistence as part of a targeted espionage campaign has been linked to the Chinese-speaking Winnti advanced persistent threat group (APT41). Kaspersky, which codenamed the rootkit MoonBounce, characterized the malware as the "most advanced UEFI firmware implant discovered in the wild to date," adding "the purpose of the | Malware Threat Guideline | APT 41 APT 41 | ||
| 2022-01-20 10:00:11 | MoonBounce: the dark side of UEFI firmware (lien direct) | At the end of 2021, we inspected UEFI firmware that was tampered with to embed a malicious code we dub MoonBounce. In this report we describe how the MoonBounce implant works and how it is connected to APT41. | Guideline | APT 41 |
To see everything:
Our RSS (filtrered)
